Latest 400-101 Dumps PDF Free Download In Lead2pass:
https://www.lead2pass.com/400-101.html
QUESTION 41
Which three of the following security controls would you take into consideration when implementing loT capabities? (Choose three.)
A. Layered Security Appoach.
B. Place security above functionality.
C. Define lifecycle controls for loT devices.
D. Privacy impact Assessment.
E. Change passwords every 90 days.
F. Implement Intrusion Detection Systems on loT devices.
Answer: ADE
QUESTION 42
Which EIGRP feature allows the use of leak maps?
A. offset-list
B. neighbor
C. address-family
D. stub
Answer: D
QUESTION 43
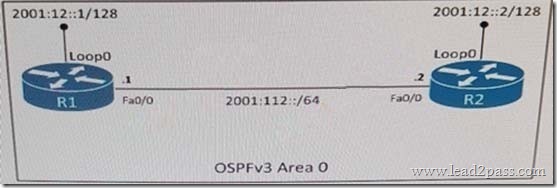
Refer to the exhibit. Which IPv6 OSPF network type is applied to interface Fa0/0 of R2 by default?
A. broadcast
B. Ethernet
C. multipoint
D. point-to-point
Answer: A
QUESTION 44
Which option describes the characteristics of a public Infrastructure as a Serveice cloud service model?
A. It is a way of delivering cloud-computing infrastructure (servers, storage, network, and operating systems) as an on-demand service.
B. It is a cloud service where the underlying hardware is managed by the cloud service provider.
C. It is a cloud-computing platform that facilitates the creation of web applications without the need to maintain the supporting software applications.
D. It is a cloud-computing platform that facilitates the creation of web applications without the need to maintain the supporting software operating systems.
Answer: A
QUESTION 45
Which effect of configuring the passive-interface S0/0 command under the EIGRP routing process is true?
A. It prevents EIGRP neighbor relationships from being formed over interface S0/0.
B. It configures interface S0/0 to send hello packets with the passive-interface bit set.
C. It configures interface S0/0 to suppress all outgoing routing updates.
D. It configures interface S0/0 to reject all incoming routing updates.
Answer: A
QUESTION 46
What is the default IS-IS interface metric on a Cisco router?
A. 255
B. 64
C. 10
D. 128
Answer: C
QUESTION 47
Which two items must be defined to capture packet data with the Embedded Packet Capture feature? (Choose two.)
A. the capture rate
B. the capture point
C. the capture buffer
D. the buffer memory size
E. the capture filter
F. the capture file export location
Answer: BC
QUESTION 48
When you configure an IPv6 IPsec tunnel, which two fields can represent the ISAKMP identity of a peer? (Choose two)
A. Authentication method
B. DH group identifier
C. Hostname
D. IPv6 address
E. Encryption algorithm
Answer: CD
QUESTION 49
Which action enables passive interfaces in RIPv6(RIPng)?
A. Use “passive-interface default” under the routing process.
B. Enable passive-interface on interface configuration.
C. passive interface are not supported in RIPng.
D. Enable passive-interface for each interface under the routing process.
Answer: C
QUESTION 50
Which statement is true about IGMP?
A. Multicast sources send IGMP messages to their first-hop router, which then generates a PIM join message that is then sent to the RP.
B. Multicast receivers send IGMP messages to their first-hop router, which then forwards the IGMP messages to the RP.
C. IGMP messages are encapsulated in PIM register messages and sent to the RP.
D. Multicast receivers send IGMP messages to signal their interest to receive traffic for specific multicast groups.
Answer: D
400-101 dumps full version (PDF&VCE): https://www.lead2pass.com/400-101.html
Large amount of free 400-101 exam questions on Google Drive: https://drive.google.com/open?id=0B3Syig5i8gpDZ0lrZUFjNWtFYlk